Brand abuse refers to the unauthorized imitation of an organization's brand. Its discovery is often a reminder to organizations that they need to protect more than just their data and IP – their reputation is at stake. But brand impersonation can also be used to launch a direct attack against the organization – and those around it.
During a first demonstration meeting recently, Darktrace PREVENT discovered a website deploying a classic trick: the letters ‘rn’ were used in sequence in an attempt to imitate the letter ‘m’ in the company’s name (e.g. “exarnple-brand.com”). Whilst obvious when you’re looking out for it, for an unsuspecting employee this goes easily unnoticed.
This website was set up by an attacker two weeks before the PREVENT demo. The website was taken down immediately, and the company was also advised to launch an internal investigation to find out if somebody had received an email from this address. The company also launched an information campaign informing their supply chain of this attack, and this last activity resulted in the discovery that one of their suppliers had been scammed through the same email domain and had transferred a large sum of money towards a shell company that was not related to the main brand. By alerting that supplier, additional money transfers were prevented.
This example is part of a broader trend being seen across the industry. ZDNET’s Fraud Trends Report found that roughly 250,000 attacks in Q2 of 2021 involved some form of brand abuse. These attacks harm companies by inflicting reputational damage, incurring financial losses from fraudulent competition, or serving as steppingstones for larger threats like supply chain attacks.
Organizations work hard to cultivate brand identities that differentiate themselves from competitors and build relationships with consumers. Yet, the stronger and more recognizable a brand is, the more often it is targeted for abuse as malicious actors take advantage of their success to reach more victims. Companies with greater online presences or international operations across multiple channels are also at higher risk.
Brand abuse takes many forms. It can be a website designed to look like it belongs to the brand to collect personal information such as email addresses and passwords. It can be an invoice sent by a vendor with a slight typo in its name. It can be an unauthorized branded webshop that never ships products to buyers. It can be a fake social media account directing customers to malicious websites that distribute malware or spreading fake news. It can be as simple as copyright or trademark infringement.

Responding to Brand Abuse
Reconquering brand reputation after a brand abuse incident can prove to be much more difficult and costly than investing beforehand to help secure the brand. Risk detection and monitoring require a holistic approach to cover the diverse forms of brand abuse, and requires patrolling the internet for copycats, typo squatters, and other malicious appropriations.

Protecting the brand identity and external attack surface can seem like a daunting task for security teams, especially in an age where monitoring internal systems proves enough of a challenge itself. Moreover, how often should the team perform this brand abuse monitoring? Companies can try to search every six months, every quarter, even every month, however there would still be gaps between when a threat actor launches an attack and when the security team discovers it. This is when AI becomes a tremendous ally, as it works at a speed and scale that human teams cannot.
The Power of PREVENT
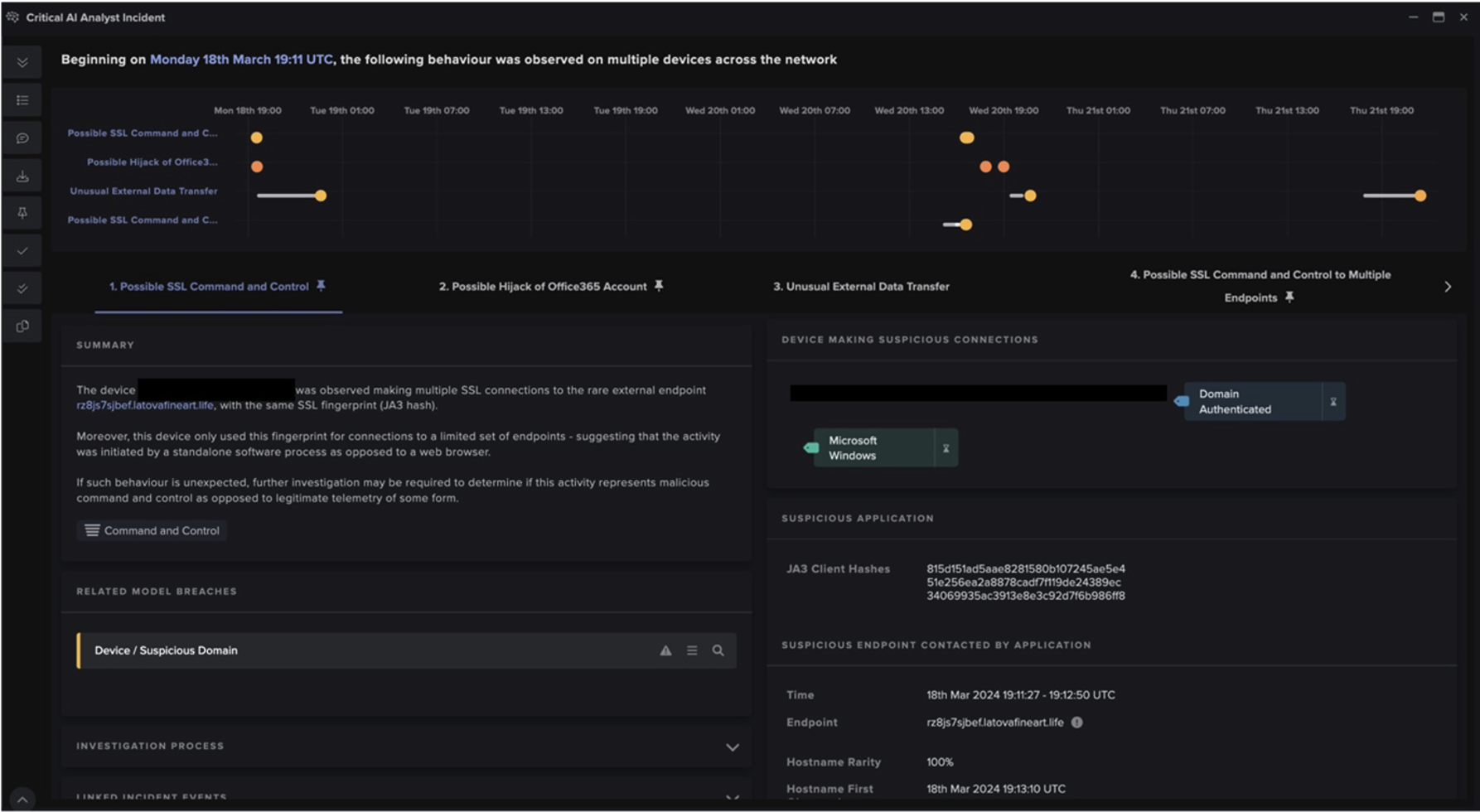
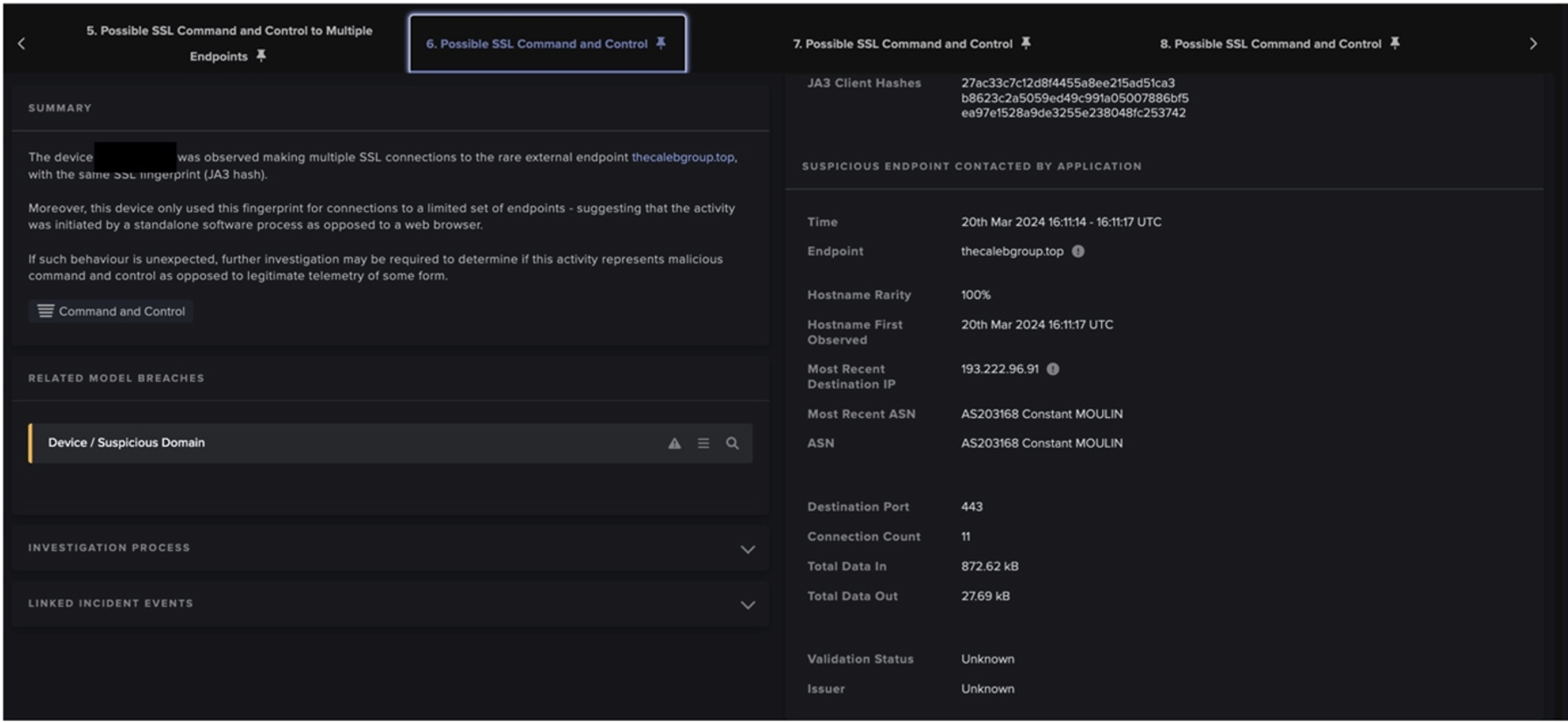
PREVENT/Attack Surface ManagementTM works autonomously and continuously to uncover instances of brand abuse, and proactively hardens defenses against any attack that might be launched as a result.
It uses AI to distinguish a company’s external assets from the rest of the global internet. Its processing features learn brand-related assets such as logos and domain names. It also leverages natural language processing and image classification algorithms to tackle even the most ambiguous and error-prone assets encountered to identify and stop copycats and typosquatters.
PREVENT/ASM carries out this comprehensive level of monitoring continuously, closing the gap between when an attacker spins up malicious infrastructure and when the security team identifies it. With PREVENT, should an attacker create a malicious website tomorrow morning, the security team will be alerted tomorrow morning.
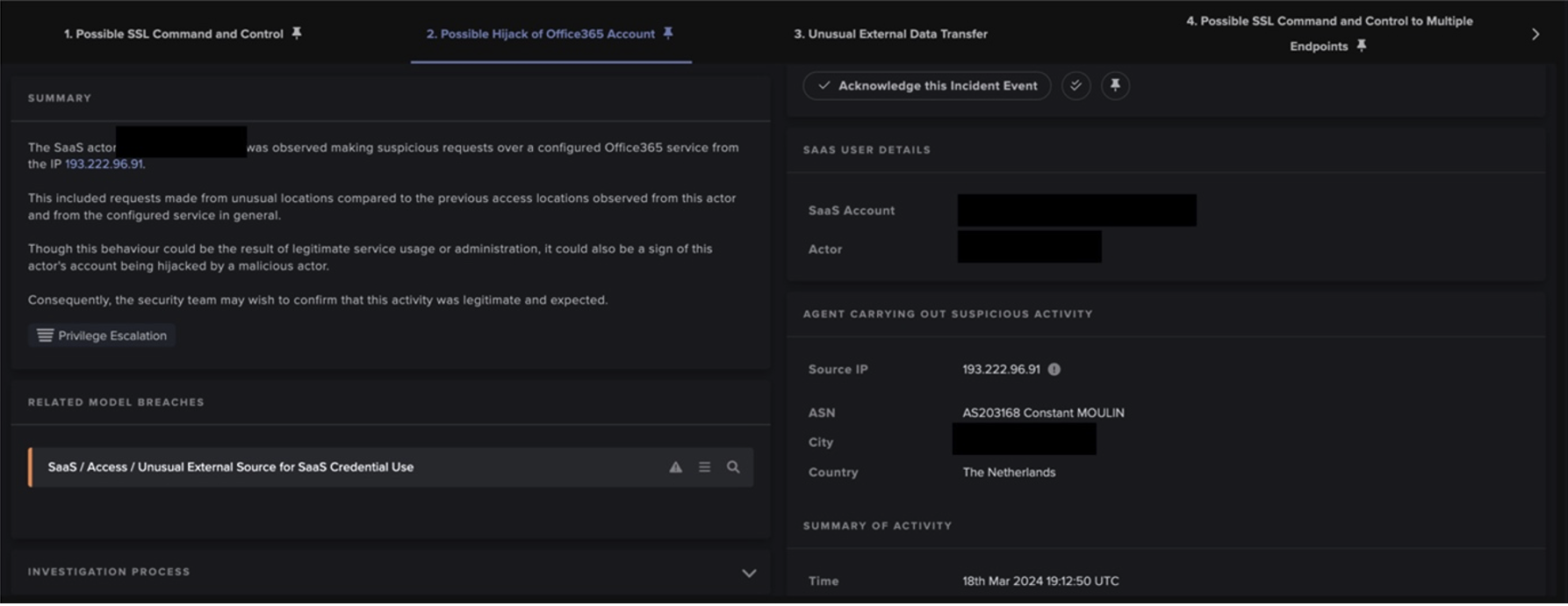
In addition to identifying brand abuse, PREVENT/ASM helps the team to collect all the relevant data needed to support a Notice and Takedown procedure. It also integrates with the rest of Darktrace’s security ecosystem to ensure that cyber defense is hardened ahead of time, should malicious assets discovered by PREVENT/ASM be used to launch an attack.
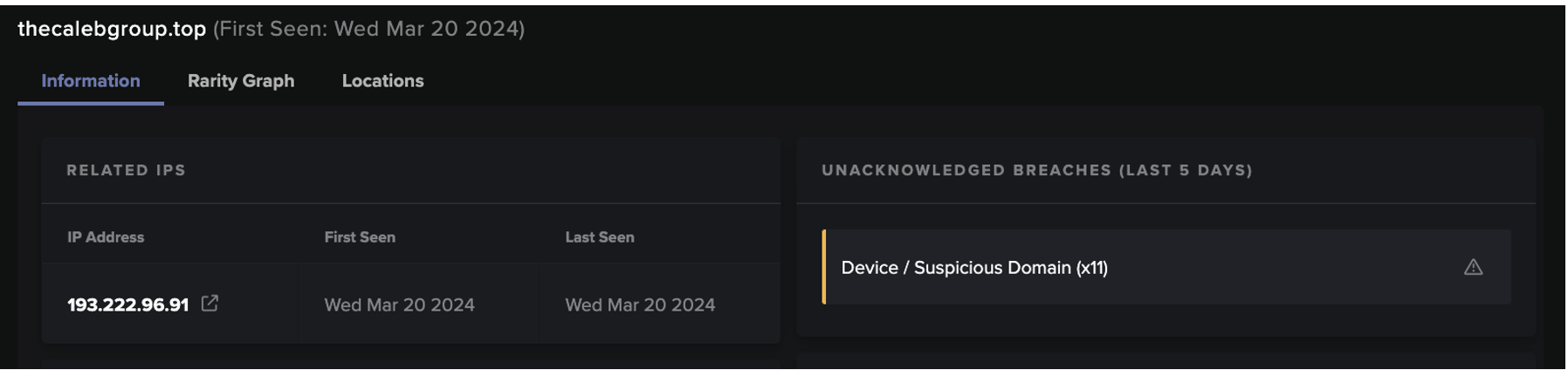
For example, identifying a webpage impersonating a brand is useful data for email security. PREVENT forewarns Darktrace/Email of malicious domains, which in turn heightens its sensitivity against emails sent from this site. The same is true with regards to network traffic as well as endpoint security: an endpoint device visiting this host will have Darktrace DETECTTM + Darktrace RESPONDTM on higher alert – ready to immediately neutralize threatening activity when it occurs.
This is the power of the Cyber AI Loop, a virtuous feedback cycle in which AI engines continuously feed into and strengthen one another.
And PREVENT not only identifies instances of brand abuse (along with Shadow IT, misconfigurations, supply chain risk, and other vulnerabilities), but it also prioritizes these risks according to exposure and potential damage and impact. With PREVENT/End-to-EndTM using Darktrace’s understanding of every device and connection inside an organization – every user and their interactions, every possible attack path – insights from the internal and external attack surface combine to give security teams a fully informed understanding of how they can spend their time most effectively to reduce cyber risk.
In these ways, PREVENT not only monitors for brand abuse at a scope and scale far beyond the capabilities of human security teams, but it also integrates with DETECT + RESPOND to harden a company’s cyber security.

























.png)