In December 2021 several CVEs[1] were issued for the Log4j vulnerabilities that sent security teams into a global panic. Threat actors are now continuously scanning external infrastructure for evidence of the vulnerability to deploy crypto-mining malware.[2] However, through December ‘21 – February ‘22, it was ransomware groups that seized the initiative.
Compromisso
Em janeiro de 2022, um cliente Darktrace deixou um servidor VMware de face externa desatrelaçado permitindo que o Cobalt Strike fosse instalado com sucesso. Vários IoCs indicam que os operadores da Cuba Ransomware estavam por trás do ataque. Graças ao serviço Darktrace SOC, o cliente foi notificado da ameaça ativa em sua rede, e a Resposta Autônoma de Antigena conseguiu manter os atacantes à distância antes de ocorrerem os eventos de criptografia.
Inicialmente o servidor VMware violou dois modelos relacionados a um download anômalo de scripts e um novo agente de usuário, ambos conectados via HTTP. Como referido em um blog anterior Darktrace , ambos os modelos haviam sido vistos em explorações anteriores do Log4j. Entretanto, como em todos os modelos Darktrace , o deck do modelo não foi projetado para detectar apenas uma exploração, variante de infecção, ou APT.

Figura 1: Darktrace modelos que quebram devido ao download do script malicioso
Investigação de analistas
Um PCAP do script baixado mostrou que ele continha um JavaScript fortemente ofuscado. Após uma investigação do OSINT, um script semelhante foi descoberto, o que provavelmente violou as mesmas regras de Yara.

Figura 2: PCAP do pedido inicial HTTP GET para o componente Windows Script

Figura 3: PCAP da resposta HTTP inicial contendo JavaScript ofuscado

Figure 4: A similar script that has been observed installing additional payloads after an initial infection[3]
Embora não seja uma correspondência exata, este código desobstruído compartilhou semelhanças com aqueles vistos ao baixar outros trojans bancários.
Tendo identificado na interface Darktrace que este era um servidor VMware, o analista isolou as conexões externas de entrada para o servidor pouco antes das solicitações HTTP GET e foi capaz de encontrar um endereço IP associado às tentativas de exploração do Log4j.

Figura 5: Logs de busca avançada mostrando conexões SSL recebidas a partir de um endereço IP ligado a explorações Log4j
Através da Pesquisa Avançada, o analista identificou picos pouco antes e imediatamente após o download. Isto sugeriu que os arquivos foram baixados e executados explorando a vulnerabilidade do Log4j.
Resposta de Antigena

Figura 6: AI Analyst revela tanto os downloads do script quanto o agente de usuário incomum associado às conexões

Figura 7: Antigena bloqueou todas as outras conexões a esses pontos finais após os downloads
Cobalt Strike
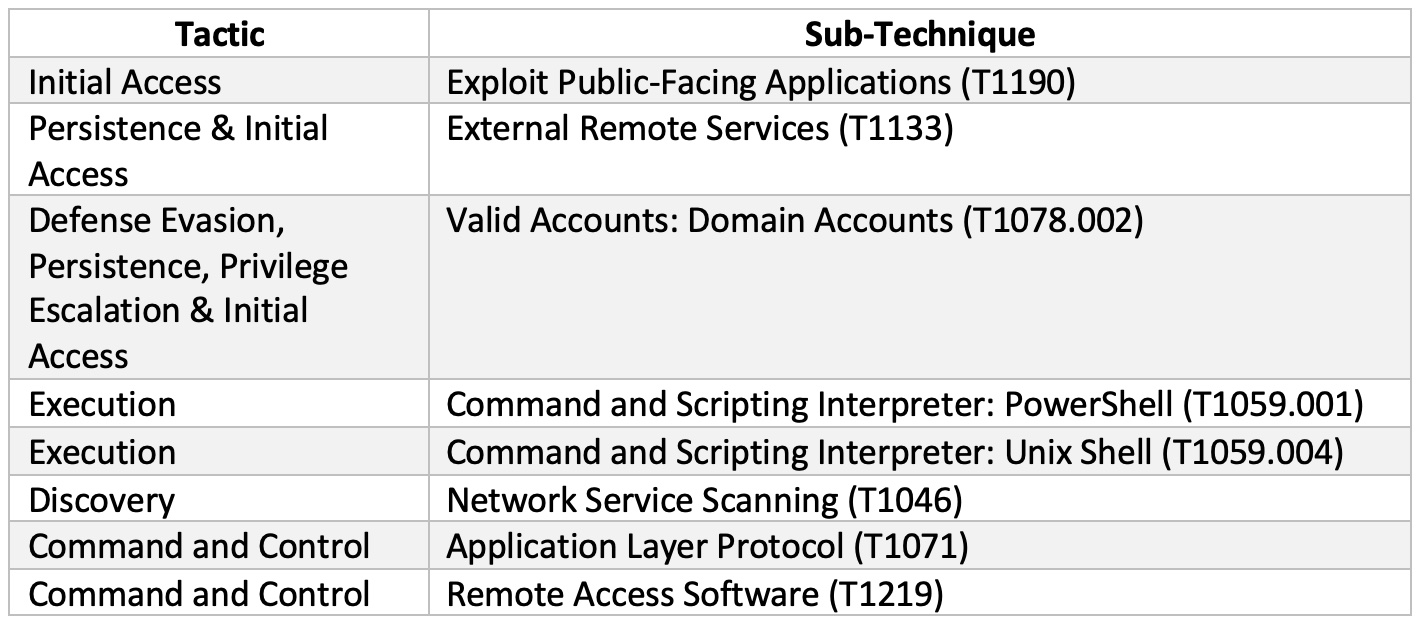
O Cobalt Strike é uma ferramenta popular para atores ameaçadores, pois pode ser usado para executar uma faixa de técnicas MITRE ATT&CK. Neste caso, o ator da ameaça tentou táticas de comando e controle para girar através da rede, no entanto, Antigena respondeu prontamente quando o malware tentou se comunicar com a infra-estrutura externa.
Na quarta-feira, 26 de janeiro, o beacon DNS tentou se conectar à infra-estrutura maliciosa. Antigena respondeu, e um analista do SOC Darktrace emitiu um alerta.

Figura 8: Darktrace detectou as solicitações DNS suspeitas e Antigena emitiu uma resposta
O atacante mudou sua estratégia mudando para um servidor diferente "bluetechsupply[.]com" e começou a emitir comandos sobre TLS. Novamente, Darktrace detectou estas conexões e o AI Analyst relatou o incidente (Figura 9, abaixo). Fontes da OSINT indicaram posteriormente que este destino é afiliado à Cobalt Strike e foi registrado apenas 14 dias antes deste incidente.

Figura 9: Resumo do analista de IA da atividade suspeita de balizamento
Simultaneamente a estas conexões, o dispositivo escaneou vários dispositivos internos através de uma varredura ICMP e depois escaneou o controlador de domínio sobre as principais portas TCP, incluindo 139 e 445 (SMB). Isto foi seguido por uma tentativa de escrever um arquivo executável para o controlador de domínio. Enquanto Antigena intervinha na gravação do arquivo, outro analista do SOC Darktrace estava emitindo um alerta devido ao aumento da atividade.

Figura 10: Resumo do arquivo .dll do analista de IA que Antigena interceptou no diretório Windows/temp do controlador de domínio
Após a última rodada de blocos de Antigena, o ator ameaçador tentou mudar os métodos novamente. O servidor VMware utilizou a Ferramenta de Acesso Remoto/Trojan NetSupport Manager em uma tentativa de instalar mais malware.

Figura 11: Darktrace revela a mudança de tática do atacante
Apesar desta escalada, Darktrace mais uma vez bloqueou a conexão.
Talvez devido a uma incapacidade de conexão com a infra-estrutura C2, o ataque parou em seus rastros por cerca de 12 horas. Graças à Antigena e à equipe SOC Darktrace , a equipe de segurança teve tempo para remediar e se recuperar da ameaça ativa em sua rede. Curiosamente, Darktrace detectou uma tentativa final de pivotar a partir da máquina, com uma incomum conexão PowerShell Win-RM a uma máquina interna. O protocolo Win-RM moderno normalmente utiliza a porta 5985 para conexões HTTP, entretanto, máquinas pré-Windows 7 podem usar o Windows 7 indicando que este servidor estava rodando um sistema operacional antigo.

Figura 12: Darktrace detecta o uso incomum do PowerShell
Cuba Ransomware
While no active encryption appears to have taken place for this customer, a range of IoCs were identified which indicated that the threat actor was the group being tracked as UNC2596, the operators of Cuba Ransomware.[4]
These IoCs include: one of the initially dropped files (komar2.ps1,[5] revealed by AI Analyst in Figure 6), use of the NetSupport RAT,[6] and Cobalt Strike beaconing.[7] These were implemented to maintain persistence and move laterally across the network.
As operadoras da Cuba Ransomware preferem exfiltrar dados para sua infra-estrutura de sinalização em vez de utilizar fornecedores de armazenamento em nuvem, porém não foi observada nenhuma evidência de atividade de upload na rede do cliente.
Pensamentos finais
Servidores VMware de face externa vulneráveis à exploração do Log4j estão sendo ativamente visados pelos atores da ameaça com o objetivo de detonação do resgate. Sem utilizar regras ou assinaturas, Darktrace foi capaz de detectar todas as etapas do compromisso. Enquanto Antigena atrasou o ataque, forçando o ator da ameaça a mudar os servidores C2 constantemente, a equipe de analistas do Darktrace retransmitiu suas descobertas à equipe de segurança que foi capaz de remediar as máquinas comprometidas e impedir a detonação de uma carga útil final de resgate.
For Darktrace customers who want to find out more about Cobalt Strike, refer here for an exclusive supplement to this blog.
Anexo
Darktrace detecções de modelos
Compromisso inicial:
- Dispositivo / Novo agente do usuário para servidor interno
- Anomalous Server Activity / Novo agente de usuário do sistema Internet Facing
- Experimento / Grande número de conexões suspeitas de sucesso
Quebras a partir de Dispositivos Críticos / DC:
- Dispositivo / Grande número de quebras de modelo
- Antigena / Rede / Ameaça Externa / Arquivo Antigena então Novo Bloco de Saída
- Dispositivo / SMB Lateral Movement
- Roteiro SMB Experimental / SMB Script Write Incomum V2
- Conformidade / Violação do modelo de conformidade de alta prioridade
- Atividade anômala do servidor / atividade externa anômala do dispositivo de Rede Crítica
- Experimental / Possível Cobalt Strike Server IP V2
Movimento Lateral:
- Antigena / Rede / Ameaça interna / Antigena Atividade Interna de Arquivo Anomaloso
- Conformidade / SMB Drive Write
- Arquivo anômalo / Interno / Executável Carregado para DC
- Experimento / Grande número de conexões com falhas suspeitas
- Compromisso / Comportamento de balizamento suspeito
- Antigena / Rede / Anomalia Significativa / Antigena Quebra de Bloco ao Longo do Tempo
- Antigena / Rede / Ameaça externa / Antigena bloco de atividade suspeita
- Conexão Anômala / Alto Volume de Conexões com Domínio Raro
- Antigena / Rede / Anomalia Significativa / Antigena Monitoramento Avançado a partir do Bloco do Servidor
Atividade de varredura em rede:
- Dispositivo / Atividade de escaneamento de SMBs suspeitas
- Experimental / Network Scan V2
- Digitalização de endereço do dispositivo / ICMP
- Atividade de escaneamento experimental / Possível SMB
- Atividade de Escaneamento Experimental / Possível SMB V2
- Antigena / Rede / Ameaça interna / Antigena Network Scan Block
- Digitalização do dispositivo / rede
- Compromisso / DNS / Possível DNS Beacon
- Dispositivo / Dispositivo de Faceamento de Internet com Alerta de Alta Prioridade
- Antigena / Rede / Anomalia Significativa / Antigena Monitoramento Avançado a partir do Bloco do Servidor
DNS / Atividade de Cobalt Strike
- Experimental / Possível Cobalt Strike Server IP
- Experimental / Possível Cobalt Strike Server IP V2
- Antigena / Rede / Ameaça Externa / Arquivo Antigena então Novo Bloco de Saída
- Antigena / Rede / Ameaça Externa / Antigena Bloco de Arquivos Suspeitos
- Conexão anômala / Novo agente de usuário para IP sem nome de host
- Arquivo Anomalous / Script de Localização Externa Rara
MITRE ATT&CK técnicas observadas
Indicators of Compromise

Obrigado a Brianna Leddy, Sam Lister e Marco Alanis por suas contribuições.
Footnotes
1.
https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-44228
https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-44530
https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-45046
https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-4104
2. https://www.toolbox.com/it-security/threat-reports/news/log4j-vulnerabilities-exploitation-attempts
3. https://twitter.com/ItsReallyNick/status/899845845906071553
4. https://www.mandiant.com/resources/unc2596-cuba-ransomware
5. https://www.ic3.gov/Media/News/2021/211203-2.pdf
6. https://threatpost.com/microsoft-exchange-exploited-cuba-ransomware/178665/
7. https://www.bleepingcomputer.com/news/security/microsoft-exchange-servers-hacked-to-deploy-cuba-ransomware/
8. https://gist.github.com/blotus/f87ed46718bfdc634c9081110d243166