Since first being discovered in May 2020, WastedLocker has made quite a name for itself, quickly becoming an issue for businesses and cyber security firms around the world. WastedLocker is known for its sophisticated methods of obfuscation and steep ransom demands.
Its use of ‘Living off the Land’ techniques makes a WastedLocker attack extremely difficult for legacy security tools to detect. An ever-decreasing dwell time – the time between initial intrusion and final execution – means human responders alone struggle to contain the ransomware variant before damage is done.
This blog examines the anatomy of a WastedLocker intrusion that targeted a US agricultural organization in December. Darktrace’s AI detected and investigated the incident in real time, and we can see how Darktrace RESPOND would have autonomously taken action to stop the attack before encryption had begun.
As ransomware dwell time shrinks to hours rather than days, security teams are increasingly relying on artificial intelligence to stop threats from escalating at the earliest signs of compromise – containing attacks even when they strike at night or on the weekend.
How the WastedLocker attack unfolded

Initial intrusion
The initial infection appears to have taken place when an employee was deceived into downloading a fake browser update. Darktrace AI was monitoring the behavior of around 5,000 devices at the organization, continuously adapting its understanding of the evolving ‘pattern of life’. It detected the first signs of a threat when a virtual desktop device started making HTTP and HTTPS connections to external destinations that were deemed unusual for the organization. The graph below depicts how the patient zero device exhibited a spike in internal connections around December 4.

Reconnaissance
Attempted reconnaissance began just 11 minutes after the initial intrusion. Again, Darktrace immediately picked up on the activity, detecting unusual ICMP ping scans and targeted address scans on ports 135, 139 and 445; presumably as the attacker looked for potential further Windows targets. The below demonstrates the scanning detections based on the unusual number of new failed connections.

Lateral movement
The attacker used an existing administrative credential to authenticate against a Domain Controller, initiating new service control over SMB. Darktrace picked this up immediately, identifying it as unusual behavior.


Several hours later – and in the early hours of the morning – the attacker used a temporary admin account ‘tempadmin’ to move to another Domain Controller over SMB. Darktrace instantly detected this as it was highly unusual to use a temporary admin account to connect from a virtual desktop to a Domain Controller.

Lock and load: WastedLocker prepares to strike
During the beaconing activity, the attacker also conducted internal reconnaissance and managed to establish successful administrative and remote connections to other internal devices by using tools already present. Soon after, a transfer of suspicious .csproj files was detected by Darktrace, and at least four other devices began exhibiting similar command and control (C2) communications.
However, with Darktrace’s real-time detections – and Cyber AI Analyst investigating and reporting on the incident in a number of minutes, the security team were able to contain the attack, taking the infected devices offline.
Automated investigations with Cyber AI Analyst
Darktrace’s Cyber AI Analyst launched an automatic investigation around every anomaly detection, forming hypotheses, asking questions about its own findings, and forming accurate answers at machine speed. It then generated high-level, intuitive incident summaries for the security team. Over the 48 hour period, the AI Analyst surfaced just six security incidents in total, with three of these directly relating to the WastedLocker intrusion.

The snapshot below shows a VMWare device (patient zero) making repeated external connections to rare destinations, scanning the network and using new admin credentials.

Darktrace RESPOND: AI that responds when the security team cannot
Darktrace RESPOND – the world’s first and only Autonomous Response technology – was configured in passive mode, meaning it did not actively interfere with the attack, but if we dive back into the Threat Visualizer we can see that Antigena in fully autonomous mode would have responded to the attack at this early stage, buying the security team valuable time.
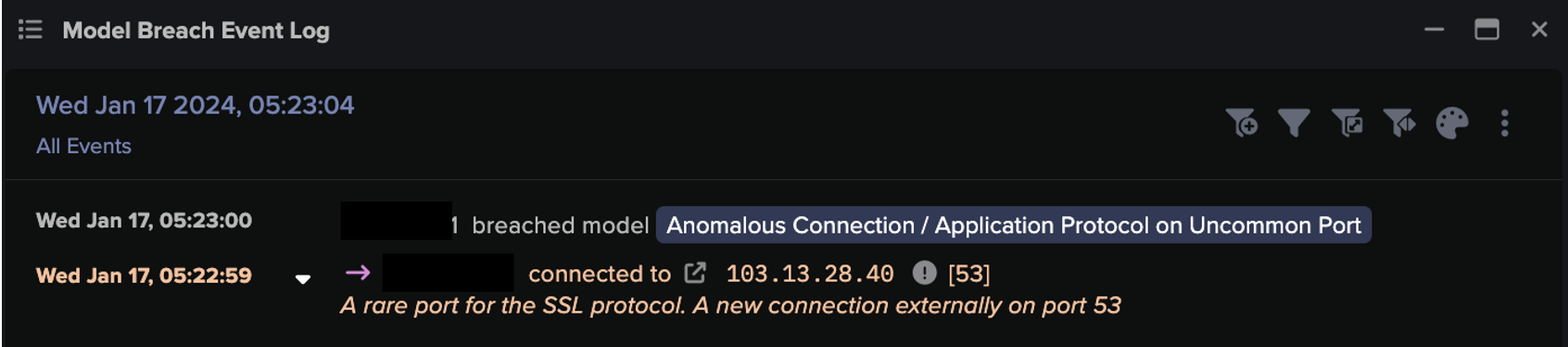
In this case, after the initial unusual SSL C2 detection (based on a combination of destination rarity, JA3 unusualness and frequency analysis), RESPOND (formerly known as 'Antigena', as shown in the screenshots below) suggested instantly blocking the C2 traffic on port 443 and parallel internal scanning on port 135.

When beaconing was later observed to bywce.payment.refinedwebs[.]com, this time over HTTP to /updateSoftwareVersion, RESPOND escalated its response by blocking the further C2 channels.

The vast majority of response tools rely on hard-coded, pre-defined rules, formulated as ‘If X, do Y’. This can lead to false positives that unnecessarily take devices offline and hamper productivity. Darktrace RESPOND's actions are proportionate, bespoke to the organization, and not created in advance. Darktrace Antigena autonomously chose what to block and the severity of the blocks based on the context of the intrusion, without a human pre-eminently hard-coding any commands or set responses.
Every response over the 48 hours was related to the incident – RESPOND did not try to take action on anything else during the intrusion period. It simply would have actioned a surgical response to contain the threat, while allowing the rest of the business to carry on as usual. There were a total of 59 actions throughout the incident time period – excluding the ‘Watched Domain Block’ actions shown below – which are used during incident response to proactively shut down C2 communication.

RESPOND would have delivered those blocks via whatever integration is most suitable for the organization – whether that be Firewall integrations, NACL integrations or other native integrations. The technology would have blocked the malicious activity on the relevant ports and protocols for several hours – surgically interrupting the threat actors’ intrusion activity, thus preventing further escalation and giving the security team air cover.
Stopping WastedLocker ransomware before encryption ensues
This attack used many notable Tools, Techniques and Procedures (TTPs) to bypass signature-based tools. It took advantage of ‘Living off the Land’ techniques, including Windows Management Instrumentation (WMI), Powershell, and default admin credential use. Only one of the involved C2 domains had a single hit on Open Source Intelligence Lists (OSINT); the others were unknown at the time. The C2 was also encrypted with legitimate Thawte SSL Certificates.
For these reasons, it is plausible that without Darktrace in place, the ransomware would have been successful in encrypting files, preventing business operations at a critical time and possibly inflicting huge financial and reputational losses to the organization in question.
Darktrace’s AI detects and stops ransomware in its tracks without relying on threat intelligence. Ransomware has thrived this year, with attackers constantly coming up with new attack TTPs. However, the above threat find demonstrates that even targeted, sophisticated strains of ransomware can be stopped with AI technology.
Thanks to Darktrace analyst Signe Zaharka for her insights on the above threat find.
Learn more about Autonomous Response
Darktrace detecções de modelos:
- Conformidade / Violação do modelo de conformidade de alta prioridade
- Compliance / Weak Active Directory Ticket Encryption
- Anomalous Connection / Cisco Umbrella Block Page
- Atividade anômala do servidor / atividade externa anômala do dispositivo de Rede Crítica
- Compliance / Default Credential Usage
- Compromise / Suspicious TLS Beaconing To Rare External
- Anomalous Server Activity / Rare External from Server
- Device / Lateral Movement and C2 Activity
- Compromise / SSL Beaconing to Rare Destination
- Device / New or Uncommon WMI Activity
- Compromise / Watched Domain
- Antigena / Network / External Threat / Antigena Watched Domain Block
- Compromise / HTTP Beaconing to Rare Destination
- Compromise / Slow Beaconing Activity To External Rare
- Device / Multiple Lateral Movement Model Breaches
- Compromise / High Volume of Connections with Beacon Score
- Dispositivo / Grande número de quebras de modelo
- Compromise / Beaconing Activity To External Rare
- Antigena / Network / Significant Anomaly / Antigena Controlled and Model Breach
- Anomalous Connection / New or Uncommon Service Control
- Antigena / Network / Significant Anomaly / Antigena Significant Anomaly from Client Block
- Compromise / SSL or HTTP Beacon
- Antigena / Rede / Ameaça externa / Antigena bloco de atividade suspeita
- Antigena / Rede / Anomalia Significativa / Antigena Quebra de Bloco ao Longo do Tempo
- Compromise / Sustained SSL or HTTP Increase
- Unusual Activity / Unusual Internal Connections
- Digitalização de endereço do dispositivo / ICMP